On April 8, Windows XP SP3 will join XP SP2, Windows 2000 and Windows NT in reaching an end-of-life (EOL) status or, as we say in security terms, "attaining a state of persistent vulnerability.”
Much has been written about the change in status for Win XP SP3, from forecasting an imminent doom to declaring it a non-event. The reality is that when Microsoft pulls the plug on its Windows XP operating system, it will leave many municipalities and other facilities more vulnerable to hackers. For example:
• There are at least 168 hacking risks with XP right now. Many of these run in automated hacking tools, making it easier to attack.
• Even one XP machine on your network provides a backdoor for attackers.
• These hackers can easily scan your network to find XPs and attack them.
A risky choice
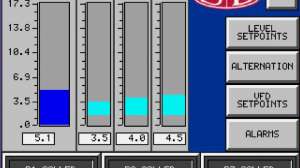
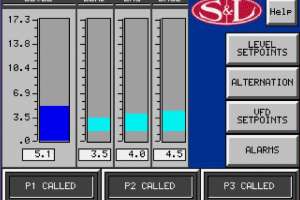
Because about 30 percent of the installed base of computers using Windows are running some version of Win XP and, by our estimate, more than half of those are part of an industrial control system (ICS) or SCADA system, what should users expect this week and beyond?
Windows XP systems will run relatively the same in the coming months as they are running right now. The Win XP EOL is not comparable to a year 2000 bug, and it will certainly not cause computers to fault or start producing errant calculations. It simply means there will no longer be regular patches for flaws — security or otherwise — in the Windows XP software. Win XP SP2 reached EOL in 2010, and many of those systems continue running to this day. Applications written for Win XP should continue to run — and might even enjoy continued support from their vendors — without interruption.
However, choosing to run an EOL version of Win XP is risky. Today, Win XP SP2 is as vulnerable to the Stuxnet delivery exploits and malware as it was in 2010. In fact, Win XP SP2 is a known target for malware and exploit developers.
What concerns security professionals is that with an EOL status, any Win XP vulnerabilities will be permanent — no fixes or patches are forthcoming. A further worry is that with the EOL announced many months ago, criminal hackers have been sitting on discovered vulnerabilities in hopes that they won’t be patched before the EOL arrives. These vulnerabilities will then be easily and readily converted into zero-day exploits that can attack a third of the world’s computers with little to deter them.
Anti-virus not enough
But won’t anti-virus software provide protection? Signature-based AV software might help, but only after the malware has been discovered by security researchers and AV publishers. If the malware spreads rapidly or isn’t detected by AV vendors before your system is compromised, AV software will be inadequate protection for these Win XP systems.
Also, ICS installations typically delay rolling out updated AV files and AV engine upgrades until they can be tested on a local development system (a fine practice, by the way) or by their vendors. So, the period in which your Win XP systems will be unprotected from the new malware may be further extended.
So, what is a concerned Win XP user to do? Consider the following:
• Start by hardening these systems and limiting their connections to non-ICS computers (including smart phones) and removable media (USB drives, CDs, DVDs)
• Patch these systems to Win XP SP3 along with all recent patches currently available.
• Stop using the administrator account for anything but configuring and administering the computer. Rename this account and choose a good password (difficult to type but easy to remember). Limit or remove nonessential users from the admin group.
• Stop using these systems for Internet-related activities, like browsing and email. Remove these programs — even currently supported versions — so they will not have access to vulnerable operating system services and functions in Win XP.
• Review your firewall rules, especially regarding outgoing packets, so that only essential traffic is allowed.
• Ensure that your backups are successful and readily available so there are viable restore points, if necessary.
• Consider adding a whitelisting product to your ICS. You will need to involve your ICS vendor (and probably your IT security team) in the decision to find the best-supported option for your system.
• Start planning now to replace these systems with more modern computers and operating system versions. You will achieve a step change in performance and security in the process.
Sharp-eyed readers will note these are the same measures security professionals have recommended for years. The EOL of Win XP provides an occasion for you to improve the security posture — and resiliency — of your ICS by putting needed attention on best practices for this specialized computing environment in your plant.
Jonathan Pollet is founder and executive director of Red Tiger Security, a focused SCADA Security consultancy based in Houston, Texas. Visit www.redtigersecurity.com.